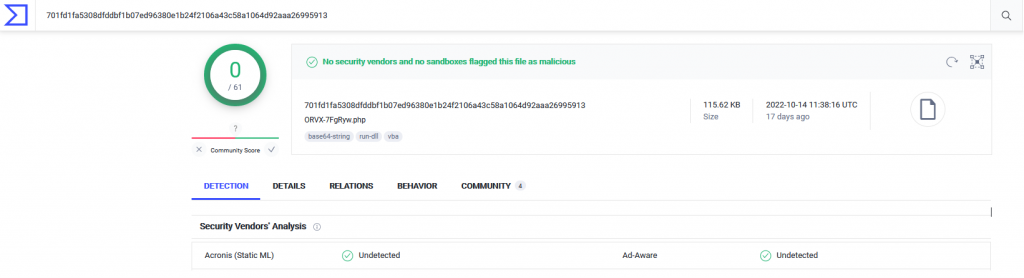
A few weeks ago investigating an incident I came across a web shell which is still not being detected by any Antivirus Solutions on the market.
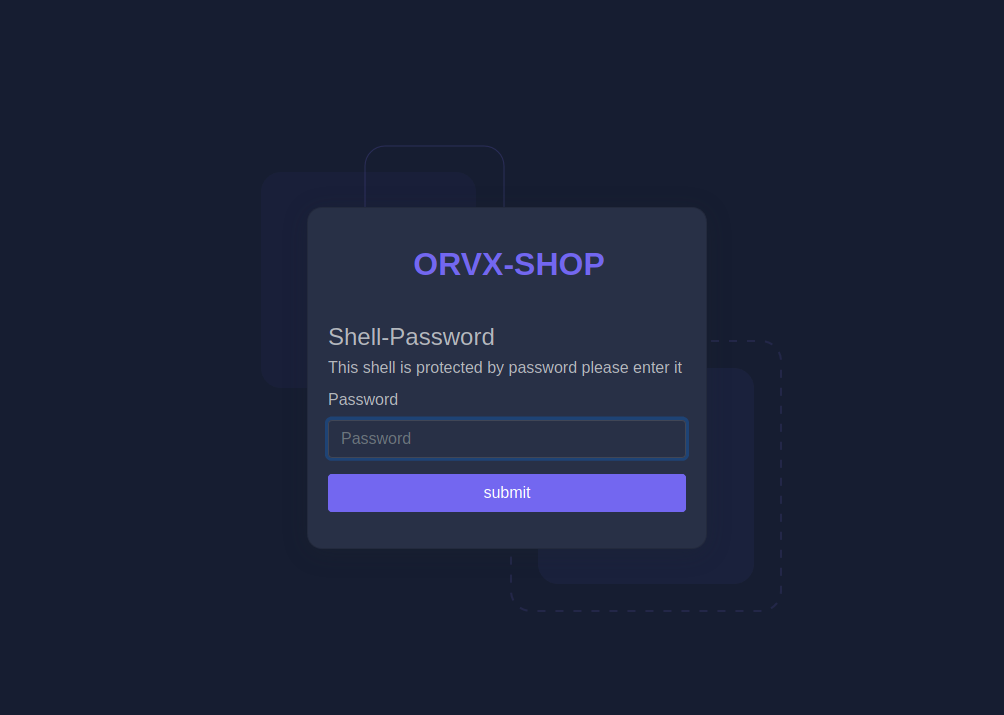
The design of the web shell landing page looks very polished and professional whilst the inner workings of the shell follows a similar framework as the Web shell by Orb (WSO) shell.
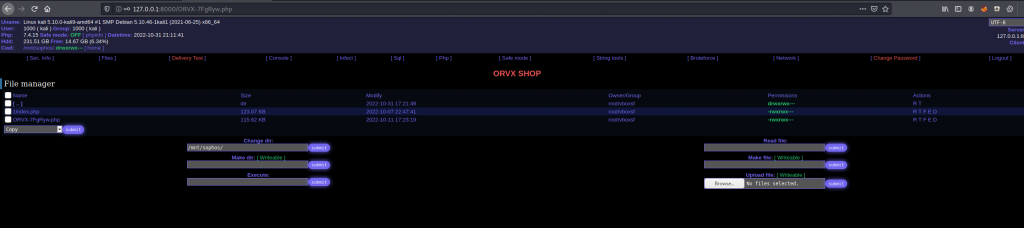
Once analyzing the code the threat actors left a comment at the top of the page reading /* Visit our shop orvx.pw - Shell v3 NEW! Checksum: 017ee37259e76d18845f23ab863d787883b3739c */. When visiting the orvx.pw website I discovered this was a one stop shop to purchase all that is required to launch a phishing attack. This website does not sit on the dark web but is available on the normal internet (surface web) that anyone can access readily.

As you can see they only accept payment methods by cryptocurrencies and digital currencies such as perfect money. Within this platform the sale of compromised cPanel hosts are being sold by sellers for as little as $8.00 per shell. Essentially you are buying access to the webshell that the original threat actor has left on the infected account. Once you have access to the shell like webshell By orb you can start exfiltrating data from the user or use the platform for phishing and spamming. On the shopping page you can also narrow down your search for a particular host you want to purchase web shells on.
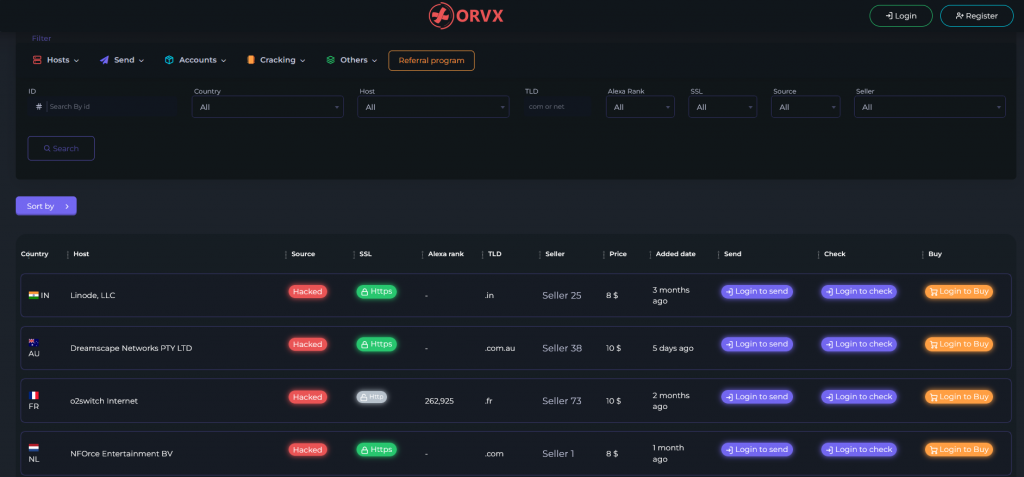
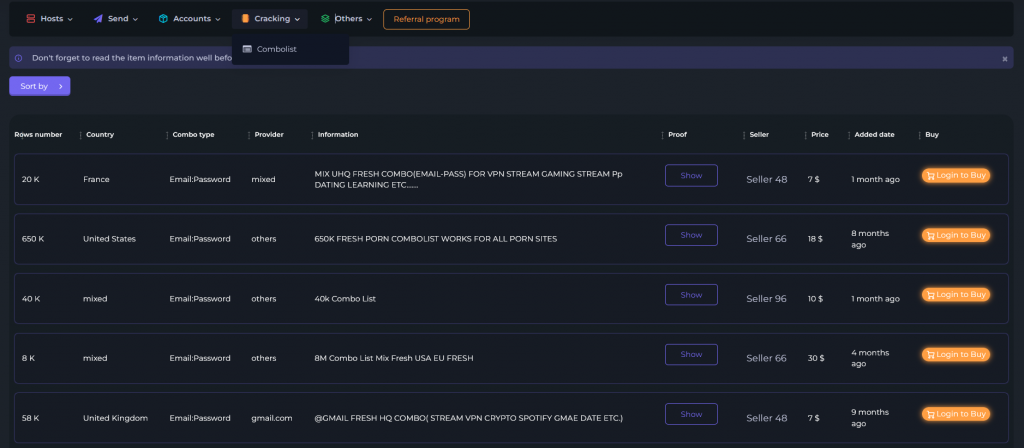
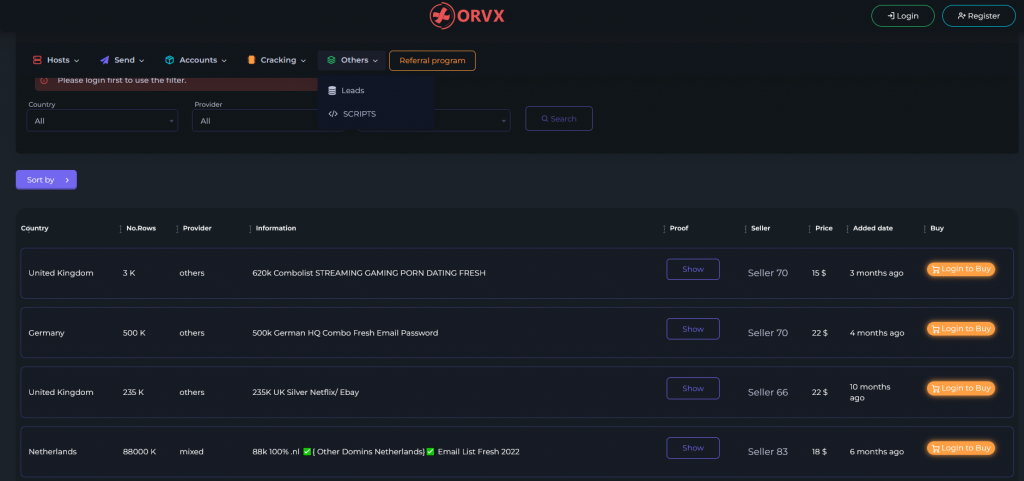
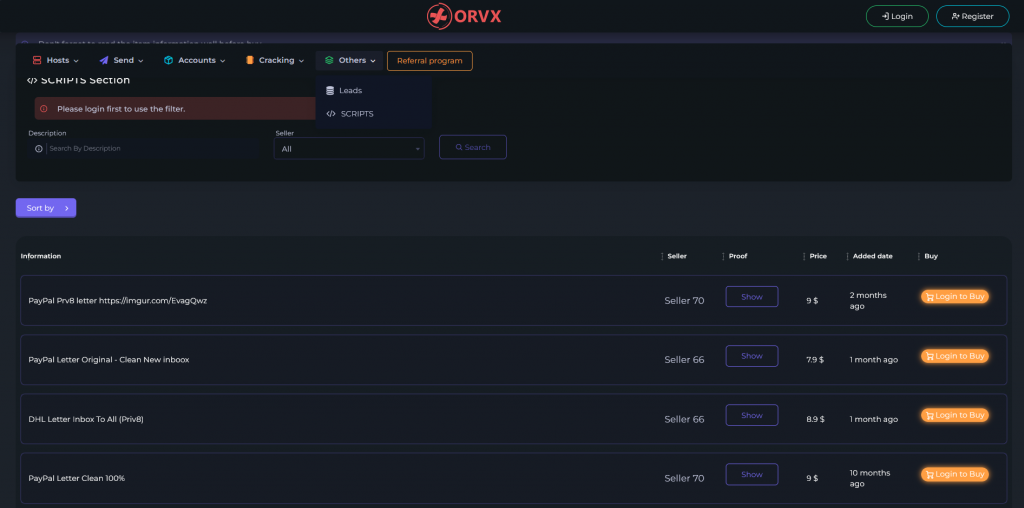
This store front does not stop there. They also sell combo lists (usernames and passwords). Lead lists (blocks of email addresses to a particular provider) and scripts (the frame work for a phishing attack).
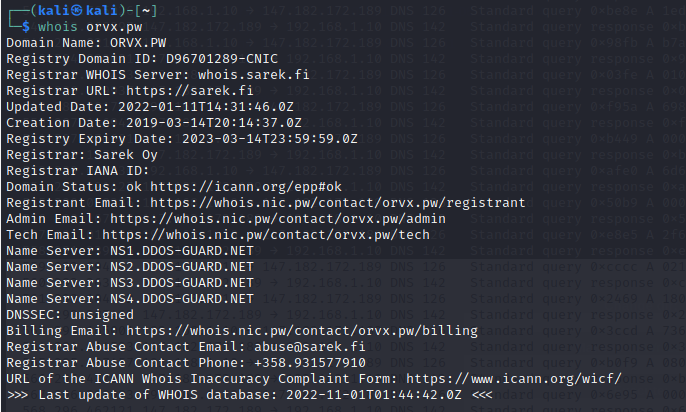
The website itself is being protected by a Russian DDoS provider called DDOS-Guard.net and was previously protected by Cloudflare
The point of the blog post is to bring light to operations like this so people are aware and Security Experts can take action and make our internet a safer place for everyone.